IP blocking on PfSense with CrowdSec

This blog post is a continuation of my previous blog post about combining CrowdSec with a Fortigate firewall. In this post I will show you how to use the same IP blocklist and use it on PfSense. In theory you should also be able to use it on OPNsense but it CrowdSec have already created a plugin to do it.
Before you read this blog post. Read extracting the blocklist in my previous blog post. Please note that cslist.domain.tld is just an example. I'm writing it instead of my personal address.
Creating the alias in pfSense
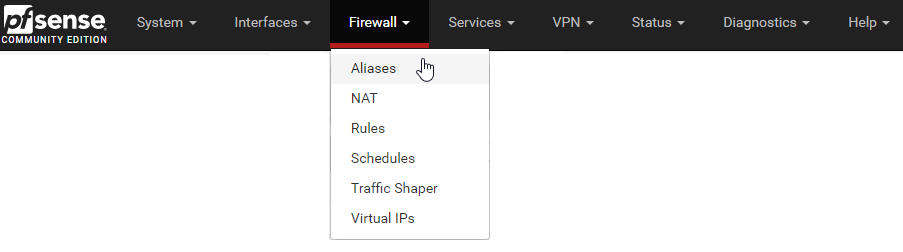
Start by going to Firewall - Alias in the top menu
Then click add at the bottom of the alias list

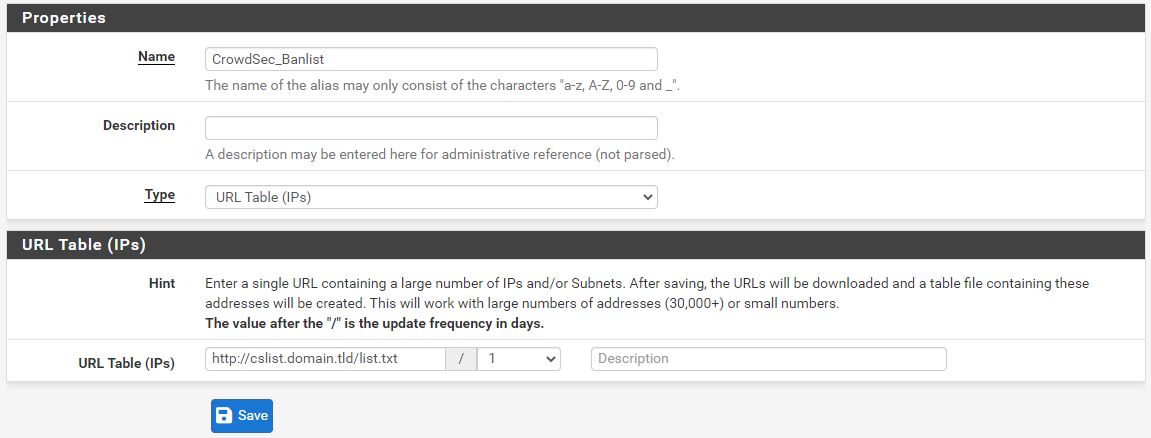
I called my new alias CrowdSec_Banlist. Type is URL Table (IPs).
At the field URL Table (IPs) I entered http://cslist.domain.tld/list.txt
The number in the field after / is how often pfsense will download the file. One time every day isn't often enough but it is a good start.
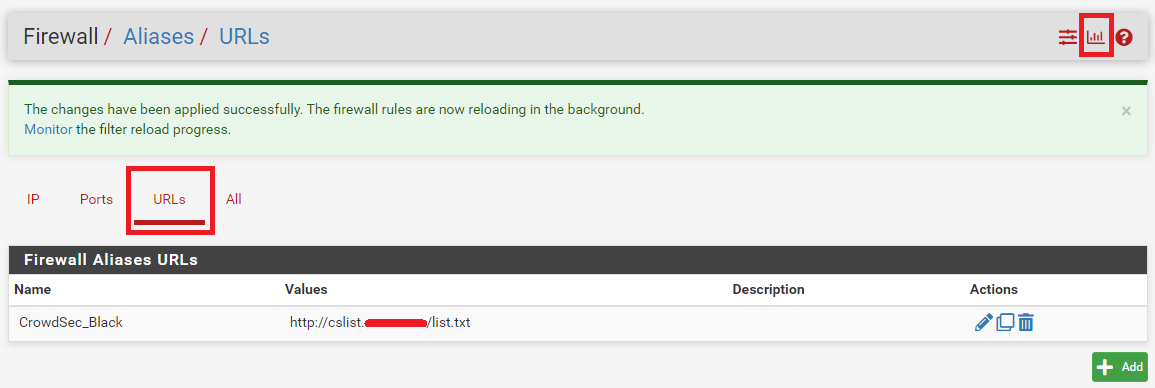
After clicking Save switch to the URL Tab if you want to verify that your list is there.
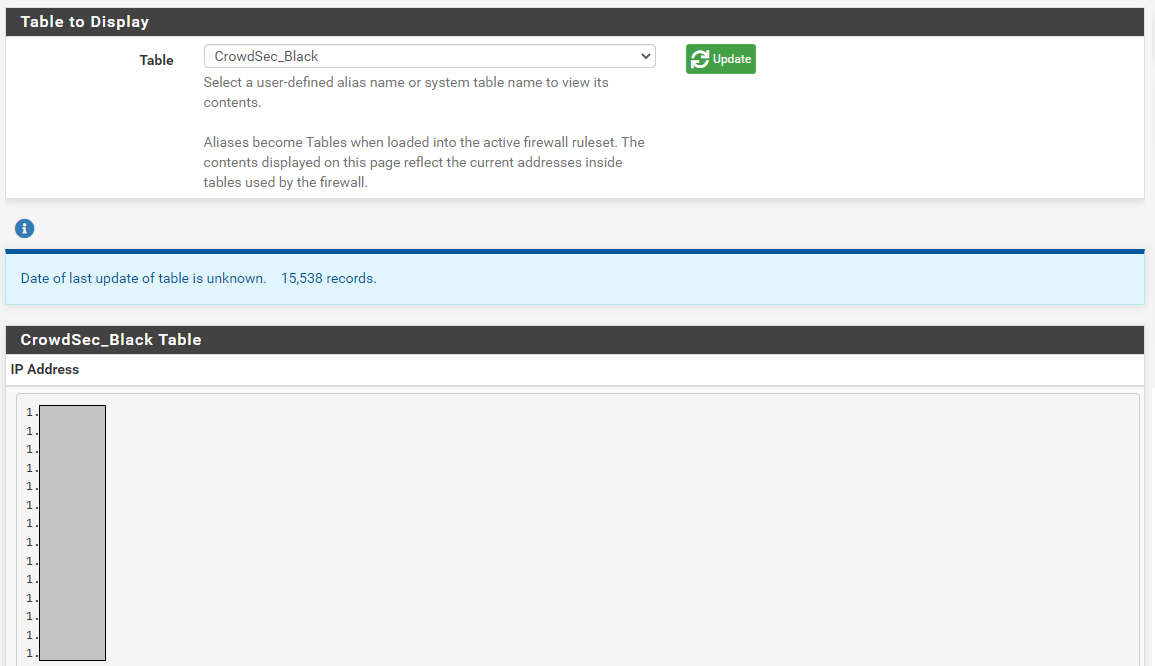
To verify that pfsense loaded your list click on the graph looking icon in the top right. That takes you to to diagnostics. Select the CrowdSec-list from the drop down menu.
Next step is to force updates of this table every 5 minutes.
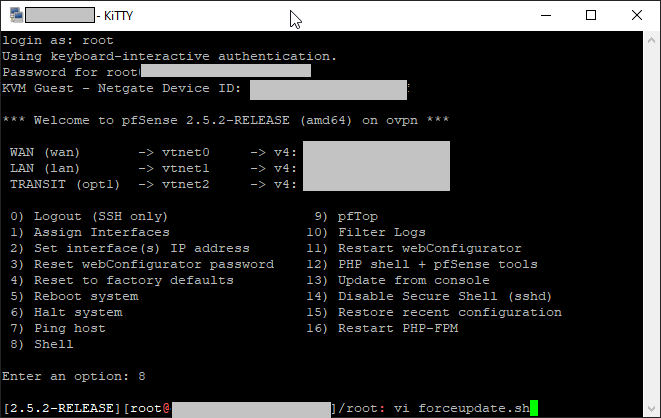
First you have to enable SSH access to your server.
The log on to the server with the root account. Select 8 to get a command prompt.
By default pfsense only downloads the file every x days. To keep track when it is time to download the new file it checks the date on the file. We can override it by changing the date on the file. First we need to double check the file name of the alias.
ls -lah /var/db/aliastables/
total 331
drwxr-xr-x 2 root wheel 3B Mar 30 08:54 .
drwxr-xr-x 15 root wheel 26B Mar 30 08:36 ..
-rw-r--r-- 1 root wheel 219K Jan 3 2010 CrowdSec_Black.txtNext we want to create a simple script. Type vi forceupdate.sh
Press I on the keyboard and then paste the following lines (right click if you use putty)
/usr/bin/touch -t 1001031305 /var/db/aliastables/CrowdSec_Black.txt
/usr/bin/nice -n20 /etc/rc.update_urltables now forceupdateThen press esc and then :wq to write and exit.
Now enter chmod +x to make the file writable. Try running it by typing /root/forceupdate.sh . You shouldn't get any error messages.
Now we need to schedule the update. To do that you need the cron package. Go to System - Package Manager and then select the tab Available Packages. Find Cron in the list and click Install
Now go to Services - Cron and click Add
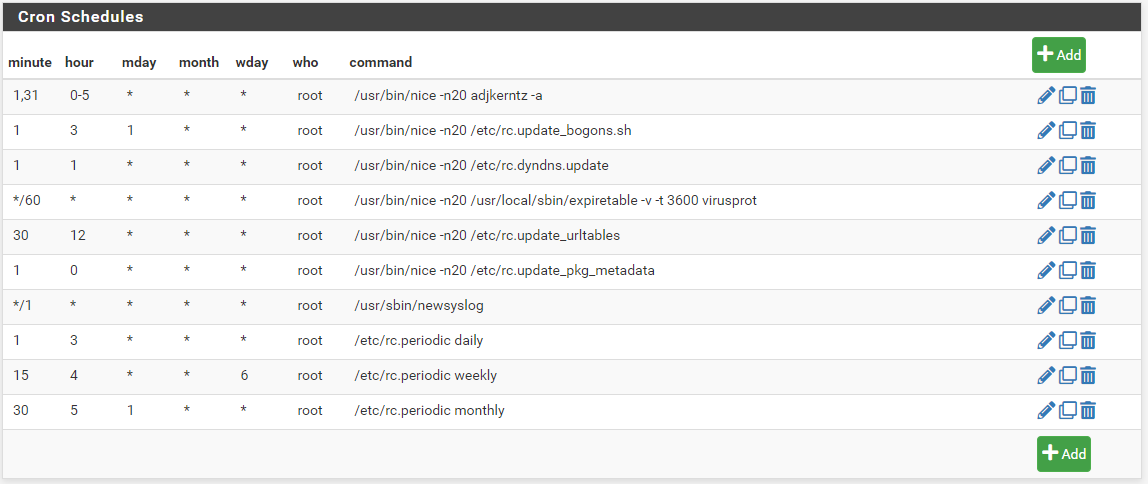
Make sure that it is the correct filename for the alias file.
If you want it to run the command every 5 minutes you write */5 in the minute box. All other time-related boxes are *. Write root as user and in command you write the path/filename to your script (/root/forceupdate.sh ). The result will look like this:
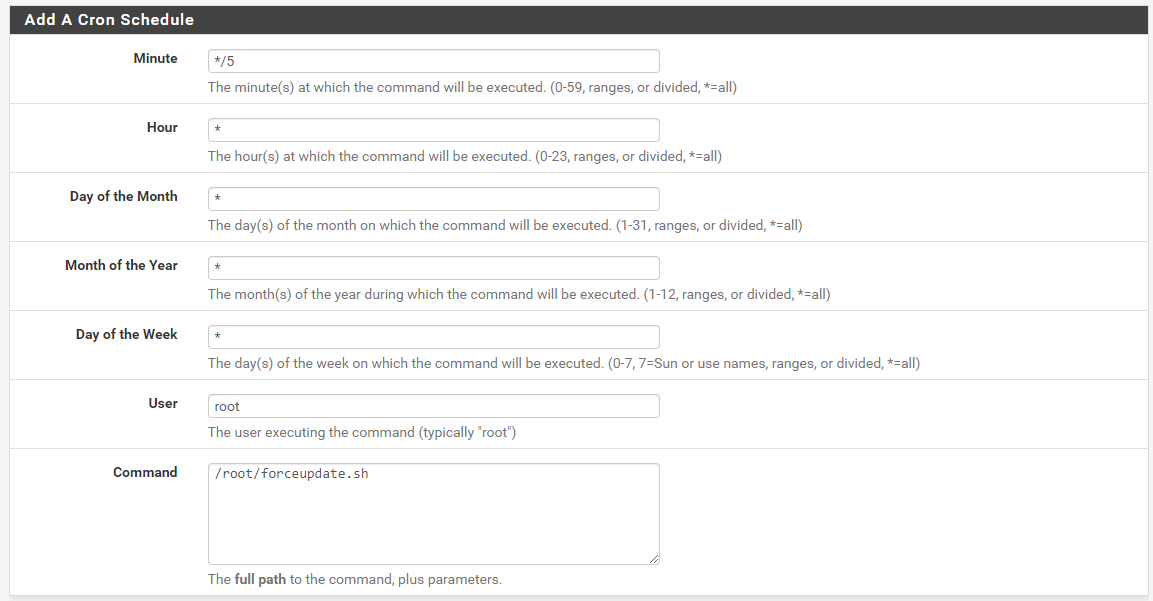
After you save you have a alias that updates every 5 minutes. Let's put it to use!
Go to Firewall - Rules and then make sure you are on the tab WAN. At the end of the page click the add button with an up arrow to add a rule at the top of the list.

Select Block as action, WAN interface, Any protocol. In source select Single host or alias and start writing Crowd and it suggests the full name of your alias. I suggest that you give the rule a description logging and future reference.
If you want logging of everything that get blocked check Log Packets before you save.
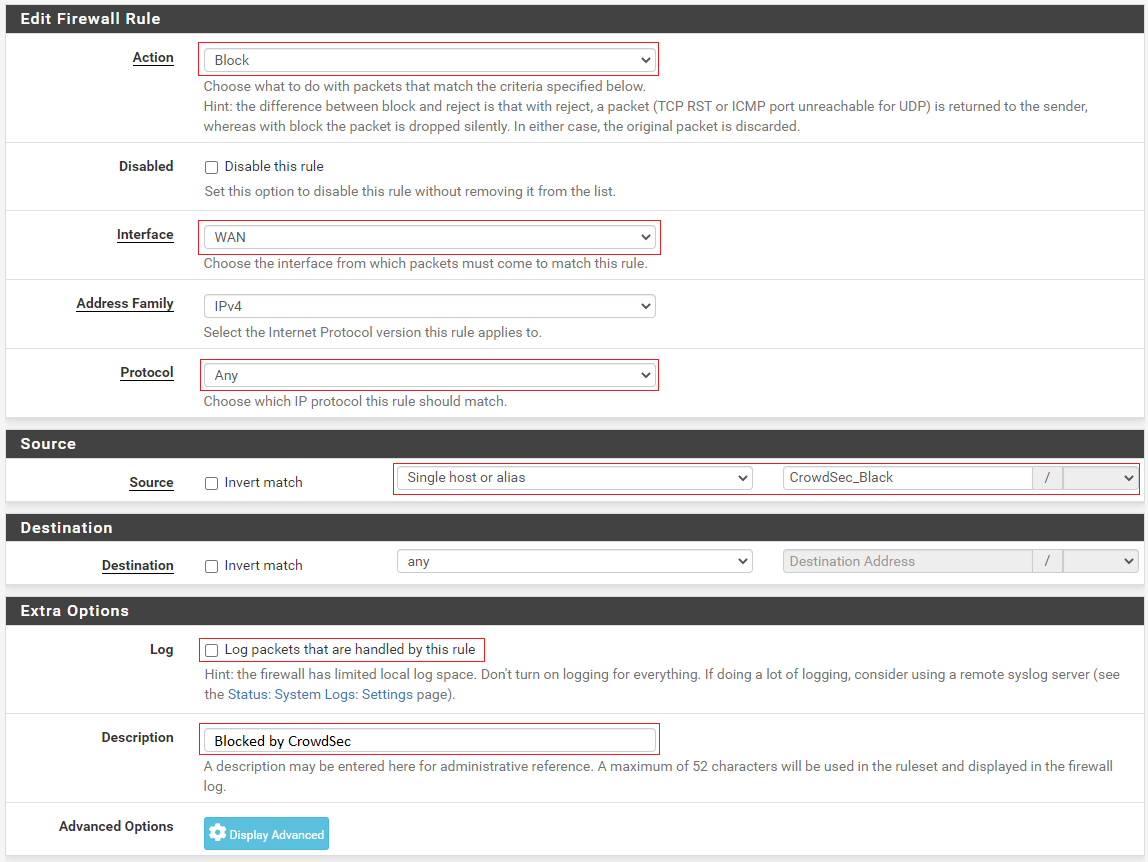
After saving the rule click activate changes.
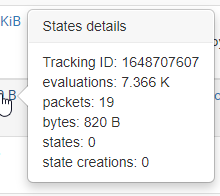
30 minutes later I can see that 19 packages have been blocked by the rule I made.
Conclusion
This was harder to figure out than on the fortigate and I had to experiment a bit before I found out what commands I should put in the script. If PfSense had the option to update every X minutes instead of hours this would have been as easy as on the Fortigate in my previous blog post.
Another way to go would be to use the list in the package pfBlockerNG but it is limited to updates every hour. If it would allow updates every 5 minutes it would be a perfect match as it also drops firewall states for established connections if the IP is on the blacklist. Crowdsec agent API support with frequent updates is on my wishlist
